Create a remote access security policy with this template
The expansion of remote work has created complicated security risks. Get help developing and updating a remote access security policy. Download our free template to get started.
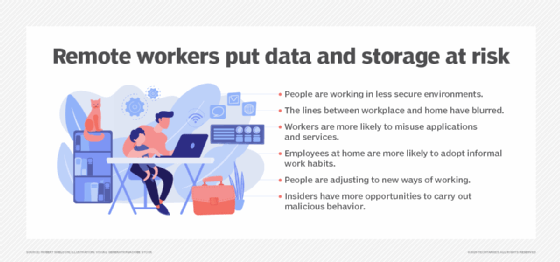
Considering the dramatic increase in remote access to IT resources during the COVID-19 pandemic, management of remote access security has become an essential activity. Organizations should establish policies and procedures for remote access security as part of an overall cybersecurity management program. While cybersecurity policies are likely to already be established and implemented in many organizations, they may not always address remote access security issues or may require updating.
This article provides guidance for preparing a formal remote access policy consistent with relevant technology standards and security best practices that will also pass audit scrutiny. Use the free, downloadable remote access security policy template included below to help prepare and document your organization's policy.
Why you need a remote access policy
Access to IT and business resources -- data, databases, systems and networks -- must be protected from unauthorized and potentially damaging attacks. Securing access to company resources from employees working remotely ensures IT assets and employees are shielded from potential disruptions. Cybersecurity measures that help protect data, systems, network configuration data, databases and other information resources are essential elements of data protection initiatives.
Remote access security includes the following infosec activities:
- ensuring access controls are strong;
- measuring the effectiveness of security controls;
- monitoring remote access activities;
- managing secure remote access technologies;
- keeping remote access rules current; and
- testing remote access security operations.
Implementing a remote access security policy is the proper starting point and should be complemented by comprehensive procedures. In addition, maintaining employee awareness of remote access security policies and best practices is an essential success factor.
How to create a remote access security policy
Remote access security policies should be developed by a cross-functional team to address operational, legal, competitive and other issues associated with remote access to information resources. The team should coordinate with internal departments for input on their remote access requirements and with HR to ensure uniform compliance by employees. Policies should be supported by senior management and should be regularly reviewed and updated.
When developing a remote access policy, make sure to define the following specifications:
- who is eligible for remote access and to what specific resources;
- which access controls and technologies will be used, such as two-factor authentication, role-based access, encryption, VPNs and other remote access technologies;
- security requirements for physical devices;
- hardware and software configuration requirements for remote access;
- frequency of change to remote access controls;
- periodic testing to ensure proper operation; and
- periodic auditing to ensure controls are being followed.
The IT department is the primary entity responsible for remote access security. When developing remote access security policies, IT leaders should consider defining the following procedures and processes:
- procedures for performing remote access using approved security controls;
- criteria for granting employees remote access;
- technologies used for remote access and minimally required security features;
- types of IT resources to be remotely accessed;
- network resources needed for remote access;
- IT employees charged with executing remote access security activities;
- emergency procedures in case of remote access security compromise;
- procedures for protecting internal company resources and employee remote assets from a data breach, ransomware attack or other cybersecurity event;
- procedures to test and validate that remote access security protocols and access controls are performing properly; and
- integration of remote access security with other data protection activities.
Capturing the above data will serve as the first step toward implementing a new, comprehensive policy for remote access security. Next, examine existing remote access security policies for policy structure and format, and use relevant components for the new policy. At this point, also determine if remote access policy elements can be added to an existing cybersecurity policy. Then, review the downloadable remote access security policy template included in this article, and adapt it as appropriate. If additional assistance is necessary, there are also software products available that can assist in preparing the policies.
Remote access security policy template
This free, editable remote access security policy template provides suggested wording for the policy and identifies areas to be completed by the policy author(s). The template can be modified in any way your policy development team sees fit.
Remote access security policy sample
A remote access security policy can be simple. In fact, a few paragraphs added to an existing cybersecurity policy may be sufficient. The policy language should define remote access security activities and how they build on existing security policies and procedures, noting the metrics discussed previously. Additional detail, such as how to test the policies, can be included if necessary.
To help format your own policy, use the following remote access security policy outline:
- Introduction. States the fundamental reasons for having a remote access security policy.
- Purpose and scope. Provides details on the policy's purpose and scope.
- Statement of compliance. Specifies laws, regulations, standards and other guidance the policy aims to achieve.
- Statement of policy. States the policy in clear, specific terms and includes the metrics stated in a previous paragraph.
- Policy leadership. Identifies who is responsible for approving and implementing the policy, as well as issuing penalties for noncompliance.
- Verification of policy compliance. Delineates metrics needed to verify that remote access security activities are verifiable and compliant with the policy and any other IT policies.
- Penalties for noncompliance. Defines penalties, including verbal reprimand or personnel file citation, for failure to comply with policy.
- Appendixes. Used as needed to incorporate additional reference data, such as lists of contacts and service-level agreements.
Refer to the sample remote access security policy template for additional guidance.
Upon completing a remote access security policy draft, it should be reviewed by IT department management and legal department, at minimum. Other relevant departments can also be invited to comment if time permits. Also, circulate the policy to appropriate internal departments and external parties, if needed. Be sure to update remote access technologies, including security provisions, if needed. Finally, deploy the approved policy, and schedule ongoing review, audit and maintenance activities.