
Sergey Nivens - Fotolia
How to maintain cybersecurity remotely during the pandemic
In the second 2020 MIT Sloan CIO Digital Learning Series, a panel of IT security leaders discussed how they are keeping their organizations secure in a COVID-19 environment.
The sudden shift to a remote work environment in the wake of the pandemic exposed organizations to more cybersecurity attacks than ever before, particularly ransomware and phishing attacks. The number of workers using personal devices on insecure home networks has created a unique opportunity for hackers and scammers to easily access and steal company data.
To mitigate the risk and ensure that data remains secure, IT security leaders are reevaluating how to maintain cybersecurity across this distributed environment.
Evaluate current security level
Organizations need a more holistic view of the partners and vendors they are working with to assess all the new risks, said Katie Jenkins, senior vice president and CISO at Liberty Mutual Insurance, who spoke during the 2020 MIT Sloan CIO Digital Learning Series.
 Katie Jenkins
Katie Jenkins
In addition to performing self-assessments of the company's security posture, Jenkins engages third-party experts to perform independent assessments and marries the two views to break down the results.
"We don't just look within -- for an organization like Liberty Mutual, we make use of a lot of trusted vendors," which is part of the risk, she said. "There is no guarantee [we're secure enough] just through our due diligence in establishing those relationships and monitoring the ongoing security that these partners exhibit."
Assessing a vendors' remote work arrangements with their employees helps Liberty Mutual figure out how to maintain cybersecurity and gain the assurance that vendors' employees are connecting to Liberty Mutual's data sets securely and following internal protocols, Jenkins said.
 Danny Allan
Danny Allan
Danny Allan, CTO at Veeam Software, said utilizing a secure software development lifecycle is an important part of ensuring workers follow the best practices associated with building software at the company.
"In a software business, you're working in an ecosystem that involves hardware you're running on [and] pulling software components from multiple different locations -- all of those have an impact on your security posture or your security stance," he said during the panel.
Veeam Software also adopted the NIST cybersecurity framework, which includes five different functions: identify, protect, detect, respond and recover. "We measure what we are doing across the organization [using] the cybersecurity framework, which is the ultimate measurement that gets passed up to the CEO [and] board of directors," he said.
 Andrew Stanley
Andrew Stanley
But it's not always about how secure the organization is, according to Andrew Stanley, the CISO at Mars, a global manufacturer of confectionery, pet food and other food products. "It's how ready are we to respond," he said.
With the increase of attacks, Stanley and his team are focusing on measuring how quickly they've been able to stop them and using scanning tools and regular penetration tests.
"You've got hundreds of thousands of systems [and] users spread in countries over thousands of facilities. There's going to be a break so [we evaluate] how quickly we can respond and recover from those incidents," he said. "That reflects how well-protected you are, how well you can anticipate security events and ultimately your ability to respond, contain and restore."
Implementing employee cybersecurity measures and exercises
As enterprises use more digital tools to support work in a remote environment, IT security leaders are figuring out how to maintain cybersecurity by taking employees through a number of exercises.
"Are we being proactive or are we being reactive?" Allan said when he discussed working with the software development teams. "You never want to be on your heels where you're reacting to things -- you want the people and process and the technology that you use to be proactive ahead of the threats that we're facing every day."
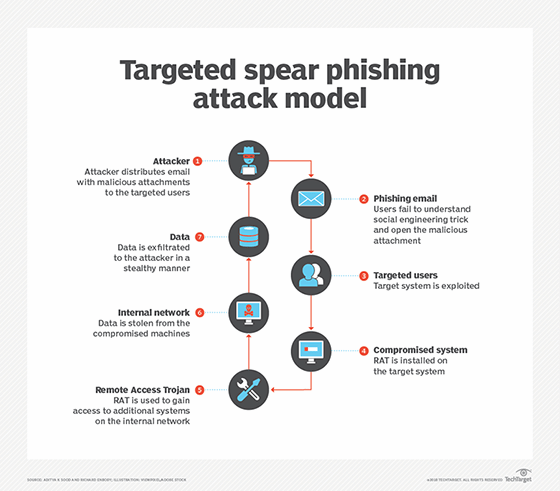
At Liberty Mutual, Jenkins continued conducting exercises to gauge employee cybersecurity awareness and ensure everyone stays sharp when it comes to detecting threats during the pandemic. For example, Jenkins' team sent employees an email branded as Zoom that requested they update their credentials. It prompted them to click a link. If an employee clicks the link, a webpage lets them know they failed the phishing exercise.
In addition, Jenkins goes through different cybercrisis exercises with the company's executive leadership teams. "It's really important for us to go through a cybercrisis tabletop exercise while we're remote and test our capabilities and decision-making in a different way," she said. "These are the kind of things that we do to help us answer that question of 'How ready are we?'"
The company also has a cybersecurity objective included as a performance goal for all employees in the technology organization, not just those with a role in security, according to Jenkins. "It recognizes the nature of shared responsibility that cybersecurity is -- if we had to go [through] this alone within the organization [and] without those partnerships, I think we would have diminished success," she said.
At Mars, Stanley also recently completed an anti-phishing exercise with the employees. The company normally conducts these exercises every six weeks but ended up waiting longer after much debate about whether to do it at all. While he wanted to take advantage of the vulnerability the pandemic caused and help educate employees, he felt it was unfair.
"In the Mars culture, that is deeply alienating because someone's going through a time of crisis, either physically or financially, and to go through and do that exercise felt like it was exploiting them," he said.
Once Stanley and his team decided to perform the employee cybersecurity exercise after 10 weeks instead of the usual six weeks, they did see an increase in vulnerability, which they were expecting, but what they also found was employees being more open to behavioral change.
"As a result of it, we saw greater engagement with training and greater conversation around training in our various social networks," he said. "What that told us is people were ready to change and were accepting change because of this crisis."







