change request
What is a change request?
A change request is a formal proposal for an alteration to some product or system.
In project management, a change request often arises when the client wants an addition or alteration to the agreed-upon deliverables for a project. The change request process should have specific procedures and protocols in place for a smooth resolution of the change.
What is contained in a change request?
Change requests may involve an additional feature, customization or an extension of service, among other things. Because change requests are beyond the scope of an original agreement or contract, this often means that the client will incur costs to pay for the resources required to satisfy the project changes.
One challenging aspect of change management is ensuring that all details in the change request form are clearly explained and all parties agree to the proposed change. Explicit and detailed documentation, such as a change request template, makes it easier to identify when a change request must be submitted.
Change requests can also originate internally (e.g., from a project team that is working with a project plan). Internal change requests can involve a variety of actions including patching and software and hardware upgrades. The change management process examines the request, determines the impact of the change (if any) and assesses which aspects of the project are impacted by the proposed change. Project team members must be familiar with the change request process to keep the project moving and on time.
What happens when a change request is received?
Once a change request has been made by employees or other stakeholders, the change control process should commence to ensure that the request is satisfied efficiently and without unnecessary use of resources.
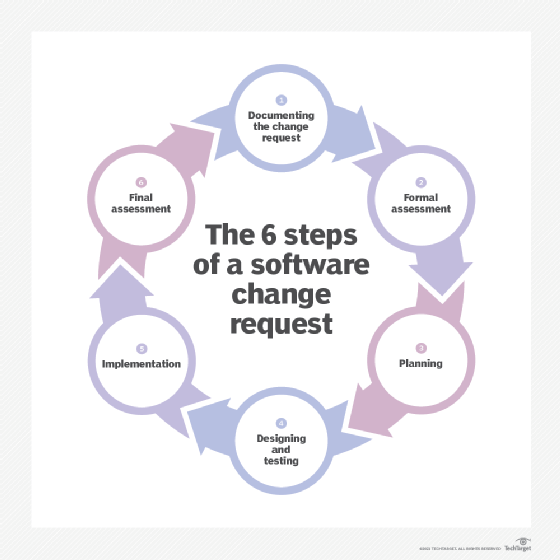
Change management policy is an essential part of a change management program and includes specific steps: receiving a request, logging it, reviewing the nature of the request, obtaining approval to pursue the request (e.g., from a change request approval panel), assigning the request to an individual/team, designing the solution, testing the changes, notifying the requesting parties of the change status if needed, completing the request (or requesting additional information), documenting what was performed and closing out the request.
What should be included in a change request form?
Several items should be included in a change request. If automation is used to manage change requests (e.g., a help desk system, the system will likely have an embedded template for change requests). Often, the template can be customized to accommodate specific requirements. Figure 1 presents a basic change request form. It requires information about the requestor, details on the request, who approved the request and the level of urgency of the request.
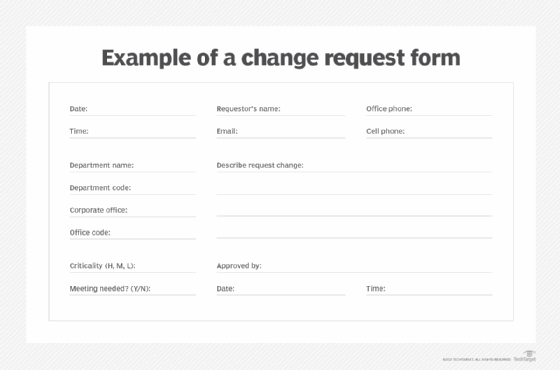
The form can ask for additional details, such as specific systems affected, location of the affected systems, or details about the business activities and processes that need to be changed. Once the request is entered in the change management process, the next step will be based on the nature of the request, its criticality, impacts on the business, staff availability and other factors.

Who can initiate a change request?
In theory, anyone inside or outside the company, if authorized, can initiate a change request. If a prospective requestor is unfamiliar with the process, the help desk or department that handles change requests, can help file the change request. If the organization has an intranet, it may contain instructions on how to prepare and submit a change request.
Importance of change requests
Change requests are not necessarily "one and done." Their value is significant for the following reasons:
- Historical record. Change requests involving specific issues can provide a running commentary on how well a system or business process has progressed over time.
- Minimize "off the cuff" requests. Verbal requests for changes often occur, and when acted on, this tends to bypass the change process.
- Official record. Change requests provide an official record of the requested change, which may be necessary if there are future disputes on how a change was completed
- Facilitates the management of change requests. Change requests often go into a pool of requests, each of which is ultimately assigned for processing. Staffing assignments may need to be modified based on the number and complexity of change requests.
- Identifies opportunities for improvement. If multiple change requests indicate a similar issue, it may be necessary to initiate a major project to change the affected system/business process.
- Change requests are audit evidence. Change requests may be requested by auditors to examine how specific activities were performed, and how changes were handled.
See also: requirements analysis, change log, IT controls
Understand the differences between IT change management vs. configuration management and explore project management tools and strategies.







