operational risk
What is operational risk?
Operational risk is the risk of losses caused by flawed or failed processes, policies, systems or events that disrupt business operations. Employee errors, criminal activity such as fraud and physical events are among the factors that can trigger operational risk.
Most organizations accept that their people and processes will inherently incur errors and contribute to ineffective operations. In evaluating operational risk, practical remedial steps should be emphasized to eliminate exposures and ensure successful responses.
If left unaddressed, the incurrence of operational risk can cause monetary loss, competitive disadvantage, employee- or customer-related problems and business failure.
What are the causes of operational risk?
The causes of operational risk can stem from people inside or outside the organization, technology, processes or even external events, including the following:
This article is part of
What is risk management and why is it important?
- Natural disasters, such as earthquakes, hurricanes or wildfires.
- Worldwide heath crises, such as the COVID-19 pandemic.
- Man-made disasters, such as terrorism, cyberterrorism and cybercrime.
- Embezzlement, insider trading, insider cybercrime, negligence and other workplace-related torts -- e.g., sexual harassment, hostile work environment, discrimination, etc.
- Regulatory compliance violations, breach of contract, antitrust, market manipulation and unfair trade practices.
- New laws or regulatory requirements -- e.g., California Consumer Privacy Act or General Data Protection Regulation.
- Failure to adhere to the company's policies or procedures or, conversely, a failure to enforce policies.
- Outdated or unpatched information technology (IT) systems and software.
- Supply chain disruptions.
- Inefficient cloud usage.
- Unfair or inconsistent work policies.
- Unsafe practices.
- Product defects.
- Human errors, such as data entry errors or a missed deadline.
- Poorly conceived or inefficient internal processes.
Decisions made by people -- human error -- tend to cause most operational risks.
What are examples of operational risks?
The above-mentioned causes of operational risks can result in one of more of the following outcomes:
- Enterprise-wide interruption, disruption or failure.
- Loss of systems control or data.
- Financial loss, including insurance claim denial.
- Safety hazards.
- Reputational damage.
- IT infrastructure damage.
- Customer churn.
- Employee churn.
- Legal liability or regulatory fines for harm caused by employees intentionally or negligently.
- Legal liability or regulatory fines for harm caused by external bad actors.
- Competitive disadvantage.
See also Basel II event categories below.
How is operational risk measured?
Two things are generally required to measure operational risk: key risk indicators (KRIs) and data. Measurement, however, can be especially challenging when organizations are unable to integrate all the diverse types of data required to understand the organization's operational risk. This might be due to the absence of software that enables the collection of data from different systems and the analysis of that data or to data silos erected by organizational fiefdoms, among other factors.
As organizations become increasingly digital, thereby utilizing more data, operational risk managers should continually monitor and assess risks in real time to minimize their potential impact.
What KRIs should businesses track? That depends on the industry in which they operate. For example, banks follow guidance from the Basel Committee on Banking Supervision (BCBS), which lays out approaches for measuring operational risk and requires banks to allocate a certain amount of capital to cover losses from operational risk. Some of the ways companies can measure operational risk, not all of which are ideal, are the following:
- Monitoring KRIs.
- Using statistical techniques.
- Using scorecards.
- Performing scenario analyses in cooperation with risk management experts and experts in lines of business to evaluate the cost and probability of specific risks.
- Monitoring customer complaints.
- Examining regulatory fines from intentionally -- or, more likely, inadvertently -- failing to report or violating a mandate.
- Assessing brand reputational damage caused by the risk, such as a data leak or breach that exposed customer data to unauthorized parties.
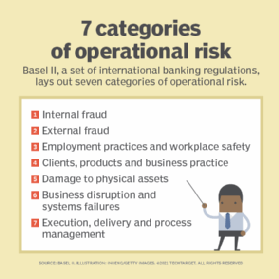
Basel II event categories
Basel II, a set of international banking regulations initially published in 2004, is the second of three Basel Accords created by BCBS. Here are the seven categories of operational risk laid out in Basel II:
- Internal fraud. Misappropriation of assets, tax evasion, intentional mismarking of positions and bribery.
- External fraud. Theft of information, hacking damage, third-party theft and forgery.
- Employment practices and workplace safety. Discrimination, workers' compensation, employee health and safety.
- Clients, products and business practice. Market manipulation, antitrust, improper trade, product defects, fiduciary breaches and account churning.
- Damage to physical assets. Natural disasters, terrorism and vandalism.
- Business disruption and systems failures. Utility disruptions, software failures and hardware failures.
- Execution, delivery and process management. Data entry errors, accounting errors, failed mandatory reporting and negligent loss of client assets.
Basel III, developed in direct response to the financial crisis, went into effect in January 2023. It continues to refine regulations that strengthen the banking industry. Among these are the adoption of minimum capital requirements, new monitoring and review standards and new leverage and liquidity requirements that aim to protect banks against risky lending practices.
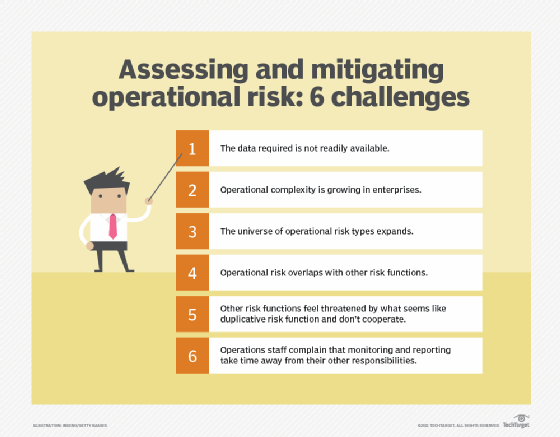
Challenges with assessing operational risk
Assessing and managing operational risk can be difficult given the following:
- The data required is not readily available.
- Operational complexity is growing in enterprises.
- The universe of operational risk types expands.
- Operational risk overlaps with other risk functions -- a symptom of its broadening definition.
- Other risk functions feel threatened by what seems like duplicative risk function and don't cooperate.
- Operations staff complain that monitoring and reporting take time away from their other responsibilities.
What are the steps in operational risk management?
Some organizations have a formal operational risk management function, while others don't. Those that have them tend to be at different stages of maturity. However, these are the steps companies follow:
- Define operational risk management, its scope, purpose and function. Keep in mind that operational risk definitions vary from industry to industry.
- Define roles that will be necessary for the function to succeed, which might involve -- but does not necessarily require -- a chief operational risk officer.
- Define operational risk management's relationship to other risk management functions cooperatively with those other functions.
- Decide the ways in which operational risk will be monitored and measured.
- Decide which tools will be necessary to enable a successful operational risk function, and determine whether those tools already exist in the organization or if additional tools are required. Procure what's necessary with the help of IT and security to avoid introducing unnecessary risk into the tech stack or unknowingly creating security gaps.
- Identify the necessary data sources and their owners; secure access to the data needed for operational risk management.
- Work with other risk functions and the business to identify process-related risks and their respective causes.
- Identify risks related to processes, such as whether they can scale as necessary or whether the processes are adequate within the context in which they run.
- Define risk categories.
- Map processes in detail, along with their risks and controls.
- Define key risk indicators.
- Ensure that each part of the organization involved in a process has been identified.
- Understand what resources are required for a process. Monitor for changes, such as the need to scale up or down.
- Understand the company's risk appetite in detail.
- Implement control measures.
- Educate the workforce about operational risks and what's expected of them as individuals. Include contact information so employees know whom to contact about a potential issue.
- Assess the impact of the operational risk management function on the business, and to the degree it involves change, ensure sound change management practices.
- Continuously measure and monitor operational risks. Use the historical data to understand trends, weak spots, etc.
Editor's note: This article was updated to reflect additional information on Basel III.
Lisa Morgan is a journalist, industry analyst and content strategist who writes and speaks about emerging technologies and their impacts on business and society, including data analytics, digital transformation, AI, data science, cloud, mobility, enterprise software and software development.







